Become a Security Specialist
Strategically secure the networks and computer systems that you look after. Identify threats and potential holes in security systems and work to fix them preemptively. Define standards, upgrade hardware, secure data. In an age where nobody deletes files but everyone demands maximum protection, security specialists are necessary for keeping our digital world running smoothly.
- 6-month long course
- 304 lessons
- 6 hours a week
- 152 hours of instruction



Mission Forecast for Security Specialists
Landing Zone
Security Specialists are in-demand and must be well trained. As technology becomes more advanced and valuable, the incentive to try and break into it also increases. This increase calls for Security Specialists in great numbers to outwit and keep any malicious actors out of your company’s data. Security Specialists will see one of the largest growths in the next 10 years, a growth of 33% up to 2030.
Mission Objective (Who’s Hiring Right Now)
Security Specialist Overview
Companies often outsource their security to larger companies, but many big companies have a security department of their own. Finding your place as a Security Specialist will not be difficult, as job opportunities continue to grow.
- + 6-month long course
- + 6 hours per week, go at your own pace
- + 304 on-demand lessons
- + 152 hours of learning materials
- + Receive a certificate confirming your training
- + Participate in real-life Virtual Lab projects
- Setup and maintain a security system.
- Manage employee login information and in-building access.
- Field security questions and ensure security.
- Train employees how to properly secure their data.
- Identify holes in current systems and analyze how to fix them.
- Protect networks and maintain them.
Prepare for Liftoff
Certified Ethical Hacker
This series of tutorial centers around Ethical Hacking, emphasizing the activity’s fundamentals, concepts, and best practices. More so, this aims to provide technical insights that will prepare hackers in getting their Certified Ethical Hacker license, an accreditation given by the EC-Council.
Introduction to Ethical Hacking
This lesson introduces the concept of hacking, putting focus on the difference of “white hat” hackers and “grey hat” hackers. More importantly, this provides a comprehensive discussion of what constitutes an ethical hacking in comparison with the unethical one. Essential hacking instruments are also outlined, giving course takers an overview of the tools and skills needed to acquire a Certified Ethical Hacker license from the EC-Council.
Operating Systems and Hacking
This lesson takes course takers deeper into hacking activities, now with the involvement of Linux and Windows, two of the most popular operating systems in the world. Centered in task automation and larger comprehension of shell scripting, this then carries an authoritative lecture about hacking terminologies, while putting into account their usage in the aforementioned operating systems.
Threats and System Hacking
This three-part lesson provides an in-depth study on hacking principles, putting emphasis on some of the best practices that one may use to easily determine internal and external threats. It then covers data collection or footprinting, which may be used to acquire information about hack prospects. Lastly, it teaches scanning and deflecting, which may be used to gather adequate data before implementing diagram method for your system.
Malware and Social Engineering
Malware comes in numerous forms, ranging from trojans and worms to viruses and backdoors. It is critical to understand how each danger differs and how to mitigate it. Wireshark examples will be demonstrated, as well as how to engage with Packets. The sociological aspect of Ethical Hacking will also be explored, while focusing on social engineering, server penetration, patch management, and counter measures.
Sessions and Web Servers
Websites come as the most susceptible to hacking activities, and this was owed mainly to their transparent, centralized, and open source-traits. This lesson then provides an overall architectural approach, which aims to understand why website hacking has become a regular occurrence. Also, recent developments, tools, measures, and penetration are brought into discussion in order for course takers to negate potential digital attacks.
Web Applications and SQL Injection
Web applications have long been a battlefield in the continuing conflict between white hat and black hat hackers. This two-part lecture, divided into 13 subtopics, investigates the new armament that both sides are utilizing to carry on with their hacking codes, as well as one of the most commonly employed attack vectors, SQL injection. Other additional learning insights that this provides includes execution of pen testing, hacking methodology, and firewall programming.
Wireless Networks and Firewalls
As much as mobile platforms have affected society as a whole, they have also fundamentally transformed the battleground between hackers and the security experts tasked with stopping them. This discussion will highlight the processes used by hackers to leverage wireless networks, aimed at targeting and negating standard security technologies such as intrusion detection systems, firewalls, and honeypots.
Cloud and Cryptography
Cloud computing's simplicity of use and scalability have been more appealing to businesses. Unfortunately, external and internal clouds are becoming the ultimate prospect for cybercriminals. This lesson carries out a comprehensive lecture that will highlight recommended practices for cryptography and encryption, as well as the specific problems that cloud computing provides for cybersecurity experts.

Mission Control
- Stay focused with a mentor’s help and support
- Build a real portfolio with Virtual Lab Projects
- Compete with classmates in a virtual classroom
- Measure your progress with the Activity Tracking Log
- Make sure you get the job with resume help and interview assistance
In Collaboration with
Chart Your Trajectory (304 videos 73 hours)
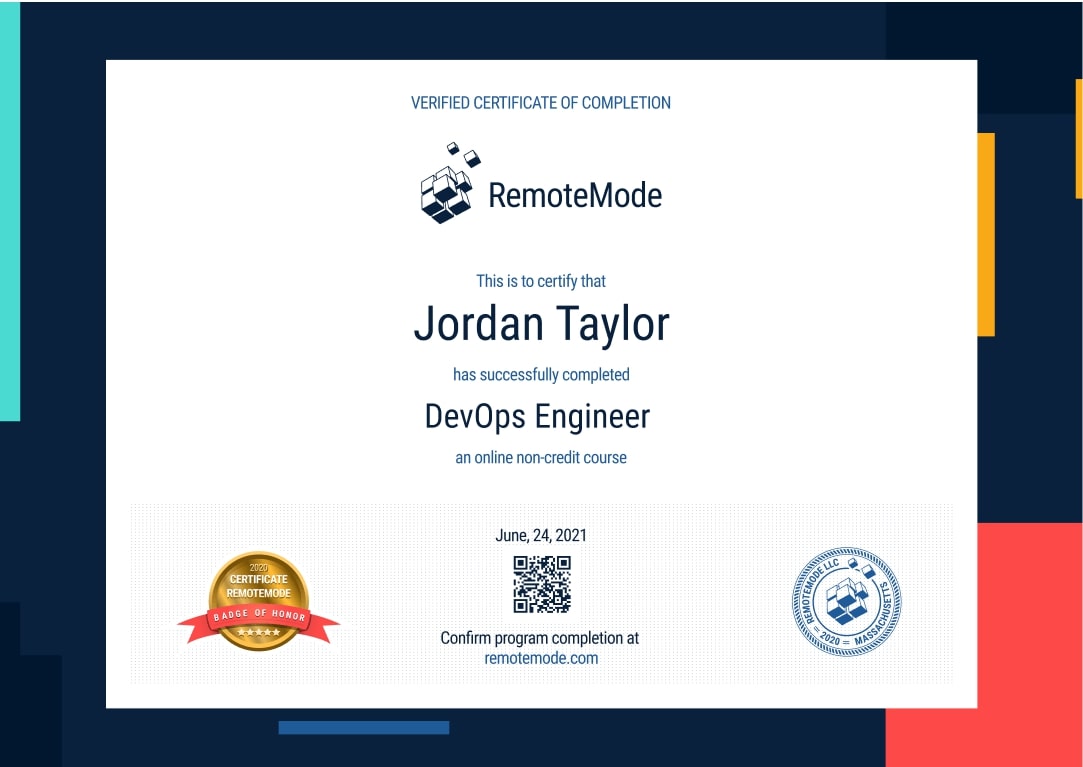
Certificate of Completion
- Receive a certificate recognized by prevalent companies confirming your training
- Complete real projects in Virtual Labs
- Go at your own pace, learn your way
- Access course videos and materials 24 hours a day
- Take practical quizzes to keep you up to speed
- Classes created and mentored by industry leaders
Grow into a Security Specialist
Help push the tech industry in a way that only security specialists can. Learn the ins and outs of tech, how to properly maintain web services and prevent attacks. Use some of the leading tools to help create programs to fight off hacks and security leaks.
Program Forecast
- 6 months long, 6 hours per week
- 304 lessons in 152 hours
- Learn at your own pace
Virtual Lab
- Real Projects
- Create a working portfolio
- Receive expert feedback and mentoring
Career Services
- Interview preparation
- Resumé assistance
- Help with LinkedIn networking
Request More Information
View pricing and financing options