Become a Security Specialist
Strategically secure the networks and computer systems that you look after. Identify threats and potential holes in security systems and work to fix them preemptively. Define standards, upgrade hardware, secure data. In an age where nobody deletes files but everyone demands maximum protection, security specialists are necessary for keeping our digital world running smoothly.
- 6-month long course
- 304 lessons
- 6 hours a week
- 152 hours of instruction



Mission Forecast for Security Specialists
Landing Zone
Security Specialists are in-demand and must be well trained. As technology becomes more advanced and valuable, the incentive to try and break into it also increases. This increase calls for Security Specialists in great numbers to outwit and keep any malicious actors out of your company’s data. Security Specialists will see one of the largest growths in the next 10 years, a growth of 33% up to 2030.
Mission Objective (Who’s Hiring Right Now)
Security Specialist Overview
Companies often outsource their security to larger companies, but many big companies have a security department of their own. Finding your place as a Security Specialist will not be difficult, as job opportunities continue to grow.
- + 6-month long course
- + 6 hours per week, go at your own pace
- + 304 on-demand lessons
- + 152 hours of learning materials
- + Receive a certificate confirming your training
- + Participate in real-life Virtual Lab projects
- Setup and maintain a security system.
- Manage employee login information and in-building access.
- Field security questions and ensure security.
- Train employees how to properly secure their data.
- Identify holes in current systems and analyze how to fix them.
- Protect networks and maintain them.
Prepare for Liftoff
CompTIA Security+
Composed of nine segments, this series aims to discuss digital and physical security. By introducing an overarching discussion, course takers will be equipped with the knowledge needed for the SY0 -501 examination.
Overview and Malware
This segment provides an introductory discussion about Security+, tapping the complex concepts of malware, ransomware, virus, and web-related infections. Divided into five parts, this lecture then provides theoretical and applied approaches to prevent these harmful web entities. As course takers go through this lesson, they will also be adept at other related concepts such as hacking, spamming, phishing, and delivery best practices.
Mobile Devices and Hardening
This next section provides a holistic discussion about security setup. Involved here are the technicalities of firewalls, intrusion detection software, and pop-up blockers while emphasizing related components such as BIOS and storage devices. In addition to this, a tutorial is provided on how to secure mobile devices by integrating more robust encryption. It then tackles different security methods such as updating and patching while focusing on the importance of policies and patch management.
Virtualization and Secure Development
Virtualization has long proven its significance, but its lasting relevance made malicious digital activities more rampant. This lecture then introduces course takers to virtual machine creation and the security measures associated with it. Next, it holds a separate discussion about security integration in different medium such as in applications and websites. Lastly, it transitions to security-related concepts of configuration, vulnerability patching, exploits, buffer overflows, SQL injection, and cross-site scripting.
Network Design and Cloud
This four-part discussion presents design practices and principles that make a network or a cloud system more functional and aesthetically appealing. It then covers pertinent concepts, including OSI model, switchers, routers, access, sub-setting, and telephony. Lastly, it covers some of the industry's best practices in handling threats, implementing perimeter security, and utilizing proxy servers.
Securing Networks
This course introduces the concepts of port and protocol, both of which are significant in harmful digital attack. Also covered are different types of cyber-related attacks, giving a comprehensive list of measures to negate transitive attacks, hijacking, spoofing, and DDOS. Other related subjects that are authoritatively presented are demonstrations of null sessions, wireless encryption, and ARP poisoning.
Physical Security and Access Control
Apart from cyber-security, this module aims to discuss security in the physical context. The usage of surveillance, technical doors, biometrics, and other security-related instruments will be discussed authoritatively. This also covers conceptual challenges that corporate, social, and medical facilities encounter. While doing so, it will then tackle pertinent processes, including authentication, access control, and best practices. The tutorial was summarized by discussing the concept of accounts and groups.
Risk Assessment and monitoring
Involved in this lecture are risk evaluations observed in qualitative and quantitative approaches. This then covers various testing techniques, including penetration and vulnerability. Not only does it run network testing, it also provides holistic intervention, including scanning, monitoring, and logging.
Cryptography and PKI
This four-part lecture comprehensively discusses the overarching concept of cryptography- its definition, technicality, implementation, and related concepts. Course takers will then understand several key points including the use and advantages of steganography and public key infrastructure.
Social Engineering and Wrap up
Contingency has been the highlight of the last part, wherein disaster planning, recovery, and redundancy are discussed. It then introduces social engineering as a concept, complete with definition and advantages. Lastly, it holds multiple lectures about engineering policies, procedures, and relationships.

Mission Control
- Stay focused with a mentor’s help and support
- Build a real portfolio with Virtual Lab Projects
- Compete with classmates in a virtual classroom
- Measure your progress with the Activity Tracking Log
- Make sure you get the job with resume help and interview assistance
In Collaboration with
Chart Your Trajectory (304 videos 73 hours)
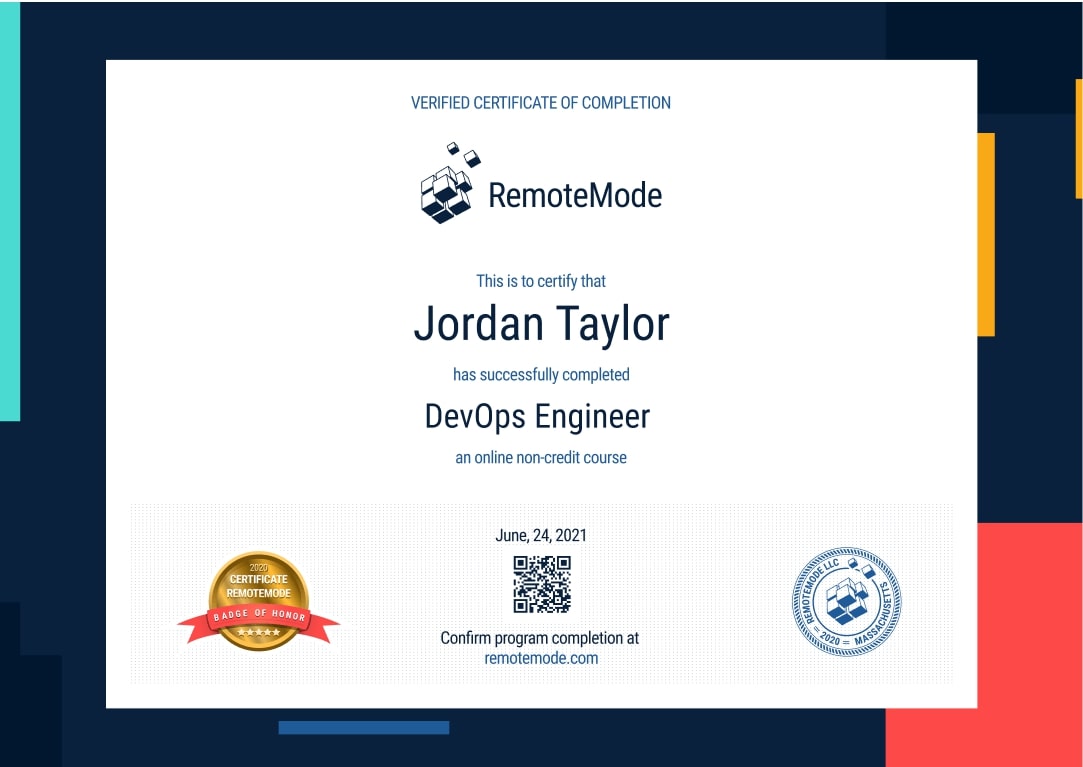
Certificate of Completion
- Receive a certificate recognized by prevalent companies confirming your training
- Complete real projects in Virtual Labs
- Go at your own pace, learn your way
- Access course videos and materials 24 hours a day
- Take practical quizzes to keep you up to speed
- Classes created and mentored by industry leaders
Grow into a Security Specialist
Help push the tech industry in a way that only security specialists can. Learn the ins and outs of tech, how to properly maintain web services and prevent attacks. Use some of the leading tools to help create programs to fight off hacks and security leaks.
Program Forecast
- 6 months long, 6 hours per week
- 304 lessons in 152 hours
- Learn at your own pace
Virtual Lab
- Real Projects
- Create a working portfolio
- Receive expert feedback and mentoring
Career Services
- Interview preparation
- Resumé assistance
- Help with LinkedIn networking
Request More Information
View pricing and financing options